How To Remove Malware
Follow these three easy steps to remove malware from your device.
1. As it happens, Malwarebytes has programs for every platform weve discussed in this article: Windows, Mac, Android, and Chromebook.
2. Run a scan using your new program. Even if you dont opt for Malwarebytes Premium, the free version of Malwarebytes is still great at removing malware. The free version, however, does not proactively stop threats from getting on your system in the first place.
3. Change all your passwords. Now that you know youre not being snooped on by some form of malware, you need to reset your passwordsnot only for your PC or mobile device, but also your email, your social media accounts, your favorite shopping sites, and your online banking and billing centers. This may sound paranoid, but with spyware, banking Trojans and the like, you just dont know for sure what data was captured before you stopped the infection. As always, use some form of multi-factor authentication and dont think you need to memorize all your passwords. Use a password manager instead.
- If your iPhone or iPad is infected with malware . Things are a little trickier. Apple does not permit scans of either the devices system or other files, though Malwarebytes for iOS, for example, will screen and block scam calls and texts. Your only option is to wipe your phone with a factory reset, then restore it from your backup in iCloud or iTunes. If you didnt backup your phone, then youre starting over from scratch.
How To Protect Against Malware
In no particular order, heres our tips on protecting against malware.
1. Pay attention to the domain and be wary if the site isnt a top-level domain, i.e., com, mil, net, org, edu, or biz, to name a few.
2. Use strong passwords with multi-factor authentication. A password manager can be a big help here.
3. Avoid clicking on pop-up ads while browsing the Internet.
4. Avoid opening email attachments from unknown senders.
5. Do not click on strange, unverified links in emails, texts, and social media messages.
6. Dont download software from untrustworthy websites or peer-to-peer file transfer networks.
7. Stick to official apps from Google Play and Apples App Store on Android, OSX, and iOS . PC users should check the ratings and reviews before installing any software.
8. Make sure your operating system, browsers, and plugins are patched and up to date.
9. Delete any programs you dont use anymore.
10. Back up your data regularly. If your files become damaged, encrypted, or otherwise inaccessible, youll be covered.
11. Download and install a cybersecurity program that actively scans and blocks threats from getting on your device. Malwarebytes, for example, offers proactive cybersecurity programs for Windows, Mac, Android, and Chromebook. Plus, our latest offering, Malwarebytes Browser Guard. Its free and its the only browser extension that can stop tech support scams along with any other unsafe and unwanted content that comes at you through your browser.
Who Does Malware Target
The answer here is: Take your pick. There are billions of consumer-owned devices out there. Theyre connected to banks, retail store accounts, and anything else worth stealing. Its a broad attack surface for adware and spyware, keyloggers, and malvertisingas well as an attractive method for lazy criminals to create and distribute malware to as many targets as possible, with proportionately little effort.
If you use your smartphone or tablet in the workplace, hackers can turn their attack to your employer.
While not currently popular with cybercriminals, cryptominers seem to be equal opportunity about their targets, going after both individuals and businesses. Ransomware, on the other hand, targets businesses, hospitals, municipalities, and retail store systems in disproportionately greater numbers than consumers.
Also, it’s not just consumers that mobile spyware criminals target. If you use your smartphone or tablet in the workplace, hackers can turn their attack to your employer through vulnerabilities in mobile devices. Moreover, your corporations incident response team may not detect breaches that originate through a mobile devices use of corporate email.
You May Like: Antibiotics For Uti Bladder Infection
Can Your Computer Become Infected With A Virus Via Email
Your computer can become infected with a virus via email, but only if you open attachments within a spam email or click on the links contained in them.
Simply receiving a spam email will not infect your computer. Just mark these as spam or junk and ensure they are deleted. Most email providers will automate this but if any slip through the net, just mark them as spam yourself and dont open them.
What Does Malware Do

Malware can crack weak passwords, bore into systems, and spread through networks. Other types of malware can lock up important files, spam you with ads, or redirect you to malicious websites. Malware attacks can result in anything from data theft to the destruction of entire systems or devices.
Malware is at the root of most cyberattacks, including the large-scale data breaches that lead to widespread identity theft and fraud. Hackers aim malware attacks against individuals, companies, and even governments.
Malware is a broad category, with different forms of malware impacting devices and systems in various ways. Lets examine some of the most common forms of malware.
You May Like: Medicine For Kids Ear Infection
How Do I Protect My Network Against Malware
Typically, businesses focus on preventative tools to stop breaches. By securing the perimeter, businesses assume they are safe. Some advanced malware, however, will eventually make their way into your network. As a result, it is crucial to deploy technologies that continually monitor and detect malware that has evaded perimeter defenses. Sufficient advanced malware protection requires multiple layers of safeguards along with high-level network visibility and intelligence.
What Can Malware Do
In short, malware can wreak havoc on a computer and its network. Hackers use it to steal passwords, delete files and render computers inoperable. A malware infection can cause many problems that affect daily operation and the long-term security of your company. Here are some of the many things malware can do.
Don’t Miss: Over The Counter Pills For Tooth Infection
What Are The Benefits Of Advanced Malware Protection
Advanced malware can take the form of common malware that has been modified to increase its capability to infect. It can also test for conditions of a sandbox meant to block malicious files, and attempt to fool security software into signaling that it is not malware. Advanced malware protection software is designed to prevent, detect, and help remove threats in an efficient manner from computer system.
Why Do Cybercriminals Use Malware
Malware encompasses all types of malicious software, including viruses, and cybercriminals use it for many reasons, such as:
-
Tricking a victim into providing personal data for identity theft
-
Stealing consumer credit card data or other financial data
-
Assuming control of multiple computers to launch denial-of-service attacks against other networks
-
Infecting computers and using them to mine bitcoin or other cryptocurrencies
Don’t Miss: Can You Get Antibiotics For A Sinus Infection
Protect Yourself Against Malware With A World
With so many types of malware out there, its harder every day to avoid them all. In addition to following all the malware prevention guidance above, you should partner with a world leader in cybersecurity. AVG AntiVirus FREE is an award-winning anti-malware tool that defends your devices against malware in real time.
Detect and block all types of malware before they infect your devices, and clear up any infections you may currently have. Plus, get always-on protection against Wi-Fi vulnerabilities and phishing attacks. Start your top-ranked protection today with AVG.
Dont Be Tricked Into Downloading Malware
Here are some tips that can help protect you from downloading software that you don’t want:
-
Only download programs from sites that you trust. If you’re not sure whether to trust a program that you want to download, enter the name of the program into your favorite search engine to see whether anyone else has reported that it contains spyware.
-
Read all security warnings, license agreements, and privacy statements that are associated with any software that you download.
-
Never click “Agree” or “OK” to close a window that you suspect might be spyware. Instead, click the red “x” in the corner of the window or press Alt + F4 on your keyboard to close a window.
-
Be wary of popular “free” music and movie file-sharing programs, and make sure that you understand all the software packaged with those programs.
-
Use a standard user account instead of an administrator account. An administrator account can access anything on the system, and any malware run with an administrator account can use the administrator permissions to potentially infect or damage any files on the system.
For more information about how to protect a computer against viruses, see Protect my PC from viruses.
Read Also: Common Urinary Tract Infection Antibiotics
Common Computer Virus Myths
- Any computer error message indicates virus infection. Error messages can also be caused by faulty hardware or software bugs.
- Viruses and worms require user interaction to activate. False. This is actually the primary difference between viruses and worms. Although viruses do require the activation of their host file in order to execute, this may be part of an automated process. In contrast, once a worm has breached a system, it can execute, self-replicate and propagate freely and with no trigger, human or automated.
- Email attachments from known senders are safe. Viruses and malware often spread by blast emailing the contacts on an infected computer. Even if you know the sender, don’t open any attachments that you aren’t sure about.
- Antivirus programs will stop all threats. While antivirus vendors do their best to stay on top of malware developments, it’s important to run a comprehensive internet security product that includes technologies specifically designed to proactively block threats. Even then, of course, there’s no such thing as 100 percent security. So, it’s important to adopt safe internet practices to reduce your exposure to attack.
How Malware Gets On Your Device
Criminals work to get malware on your devices so they can steal personal information, like your usernames and passwords, bank account numbers, or Social Security number. They use this information to commit identity theft. If you think someone may have stolen your information or identity, visit IdentityTheft.gov.
Malware can get onto your device when you open or download attachments or files, or visit a scammy website. Your device might get infected with malware through:
- downloading content available on file-sharing sites
- clicking links in fake security pop-ups sent to your computer by tech support scammers
- phishing emails that trick you into clicking on a link or opening an attachment
Recommended Reading: Do I Have A Uti Or Kidney Infection
Malwarebytes Recorded 111 Million Malware Detections On Windows Devices And 75 Million On Mac Devices In 2020 Alone Cybercriminals Are Always Trying To Figure Out New Ways To Get Malware Onto Your Computer Or Network But How Does Malware Get On Your Computer Lets Break It Down
How do you get malware infections? This isnt a one-and-done kind of response because there are many types of malware and even more ways that malware can infect your computer, devices, and larger network. SonicWall reports 5.6 billion malware attacks in 2020 this is a decrease of 43% over the prior year. But dont let this change fool you although numbers have dropped over the last year, malware is a big issue for businesses and consumers alike.
So far in 2021, weve seen the devastating impacts of malware on major organizations in the ransomware attacks on Colonial Pipelines, OmniTRAX attack, and Harris Federation. But dont think for even a moment that cybercriminals are only targeting the big guys theyre also interested in small businesses, too.
This brings us to the main question we wish to address in this article: how do you get malware? We have put together a list of malware infection methods to avoid.
Air Gap Isolation Or Parallel Network
As a last resort, computers can be protected from malware, and the risk of infected computers disseminating trusted information can be greatly reduced by imposing an “air gap” and applying enhanced controls over the entry and exit of software and data from the outside world. However, malware can still cross the air gap in some situations, not least due to the need to introduce software into the air-gapped network and can damage the availability or integrity of assets thereon. Stuxnet is an example of malware that is introduced to the target environment via a USB drive, causing damage to processes supported on the environment without the need to exfiltrate data.
AirHopper, BitWhisper, GSMem and Fansmitter are four techniques introduced by researchers that can leak data from air-gapped computers using electromagnetic, thermal and acoustic emissions.
Recommended Reading: Dr On Demand Tooth Infection
What Happens If Your Computer Is Infected By Malware
Malware or malicious software is any program designed to harm your device and data. Several types of malware including trojans, viruses, ransomware, spyware and worms can be installed on your companys computers.
Millions of people will fall victim to some malware threat in any given year, and you and your employees are no exception. But few know what exactly malware is or what happens next. Can malware get passwords? Delete programs and files? How does it really affect your business?
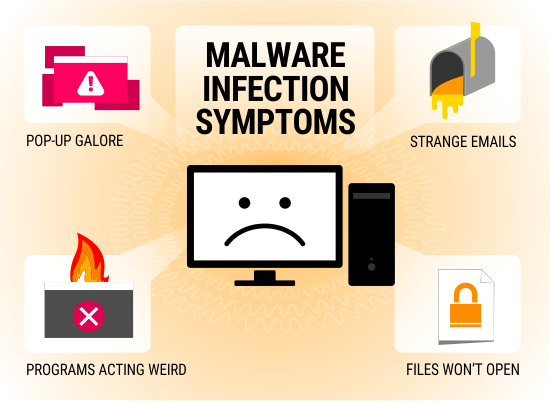
Malware works in various ways, and different types have different capabilities. Were here to guide you through how malware affects your computer, the symptoms of malware and how you can keep your business safe from a malware infection.
Protect Your Network With Consolidated Technologies Inc
When you want to leave your business network security in the hands of the experts, turn to Consolidated Technologies, Inc. Weve helped more than 2,000 businesses solve their cybersecurity concerns and protect themselves from malware and other threats.
Your network security is our top concern. Contact us to learn more about our security solutions and request your free consultation.
You May Like: Get Yeast Infection Prescription Online
An Unknown App Sends Scary Warnings
Creating and distributing fake antivirus programs is a lucrative business. The perpetrators use drive-by downloads or other sneaky techniques to get the fake antivirus onto your system, then display scary warnings about made-up threats. Naturally you have to register a payment before the fraudulent tool will “fix” the problem. And of course, scanning for malware with the fake AV is super-fast, since it’s not actually doing anything.
Your Computer Runs Slowly And Takes Longer To Start
A slow-running computer is usually the first sign of an infected computer.
If your computer used to start up quickly and run its applications with ease, be concerned if it suddenly runs very slowly and even simple tasks take a long to time execute.
Malware particularly viruses are known to slow down your system, and you should always consider the possibility of infection if your computer is running slowly.
Recommended Reading: Swallowing Pus From Tooth Infection
For How To Get Malware: Using Social Media
People of all ages love social media. Its a great way to stay connected to friends and family. Your employees may even use their work-issued devices to access their favorite social media sites. Proofpoint reports that 34% of employees admitted to viewing and posting on social media using their work devices.
Bad guys know this and use social media to send out malicious links to users. Clicking on a link in a private message can lead to serious consequences when you open it. You also might see posts for enticing product giveaways, intriguing surveys, fake job offers, and places to download free apps that are actually malicious links. These are just a handful of ways that cybercriminals can infect your computer or other devices. Proofpoint also reports that 61% of organizations experienced social media attacks in 2020.
Lets continue on our journey of answering the question how do you get malware infections? brings us to our next topic.
Latest On Coronavirus From New Scientist
Two years of covid-19:What weve learned during the pandemic so far
A soldier administers a vaccination at the Army Reserve Centre in Poole, England.
Our daily covid-19 update will resume on 4 January
Immunity offered by vaccines wanes more quickly with omicron, finds UK study
The protection conferred by booster vaccines against the omicron variant begins to wane within 10 weeks, according to a briefing released by the UK Health Security Agency .
Based on an analysis of 147,597 delta and 68,489 omicron cases, the agency found that the Oxford/AstraZeneca, Pfizer/BioNTech and Moderna vaccines are less effective against omicron than delta. For people who had two initial doses of the Oxford/AstraZeneca vaccine, the UKHSA estimates that Pfizer/BioNTech or Moderna boosters are around 60 per cent effective at preventing symptomatic infections from omicron 2 to 4 weeks after the third dose, but this falls to 35 to 45 per cent by 10 weeks. For those who had two initial doses of Pfizer/BioNTech, protection falls from 70 per cent at 2 to 4 weeks to 45 per cent at 10 weeks after a Pfizer booster, but stays around 70 to 75 per cent up to 9 weeks after a Moderna booster.
However, modelling suggests that the severity of omicron would need to be around 90 per cent lower to avoid similar levels of hospital admissions to previous waves, according to minutes from a meeting of the UK governments Scientific Advisory Group for Emergencies on Monday.
Other coronavirus news
Also Check: Get Rid Of Bladder Infection Fast
How To Tell If You’ve Been Infected:
Before you can recover from an infection, you need to find it. Below are some telltale signs that you have been infected by malware.
- You are being asked for personal information or are urged to do something urgently
- Pop-up windows, especially ones claming to be anti-virus software
- Computer gets caught in a “reboot loop”
- Computer starts playing funny sounds or starts talking to you